Agentic AI SOC
Reduce MTTR (Mean Time to Respond)
Increase Unknown Threat Detection Rate
Achieve Reduction in False Positives
Leverage AI to improve SOC Analyst Efficiency
Security threats don’t wait for your team to catch up. Hawkeye’s Agentic AI SOC autonomously detects, investigates, and responds to threats across your entire environment, closing cases in seconds, not hours
A losing Battle
Security teams today are buried under 11,000+ alerts a day, with 80% of analyst time lost to repetitive manual work.
Disconnected tools like SIEM, SOAR, EDR, and case management operate in silos, leaving teams overwhelmed.
HawkEye solves this by unifying all three into a single intelligent loop. Alerts are automatically enriched with threat intelligence and behavioral context, correlated across tools so five fragmented signals become one high-confidence case.

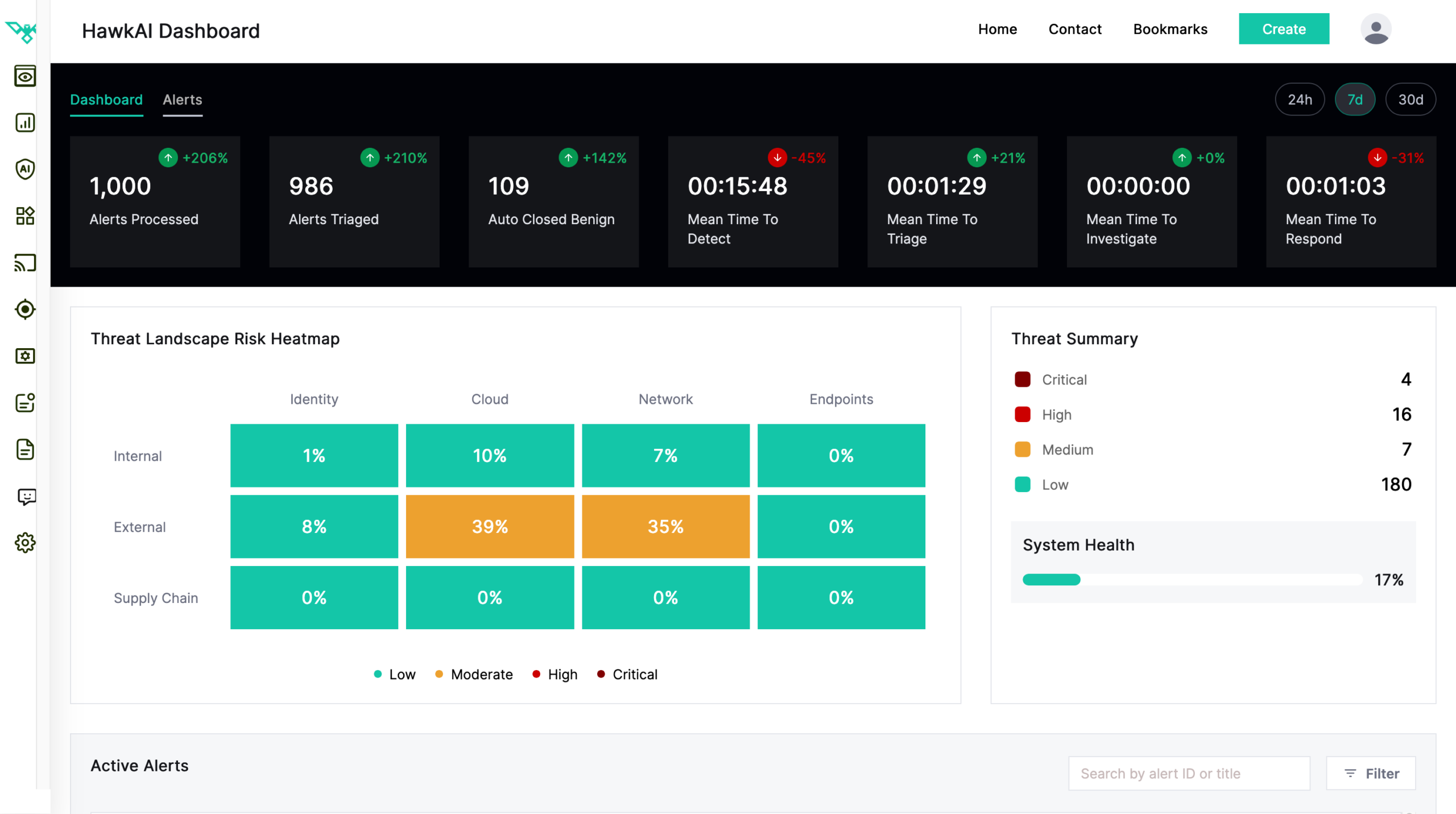
Central Command Center
Everything your SOC needs, in one place. The HawkAI Dashboard gives real-time visibility across your entire security operation.
Every metric tells a story. Alerts Processed and Alerts Triaged show the scale of what AI handles on your behalf. Auto Closed Benign tracks how much noise never reaches your analysts. The four Mean Time metrics (Detect, Triage, Investigate, Respond) measure speed at every stage of the response chain.
The Threat Landscape Heatmap gives leadership an instant read on risk across Identity, Cloud, Network, and Endpoints. And System Health keeps SOC managers confident the platform is operating at full capacity.
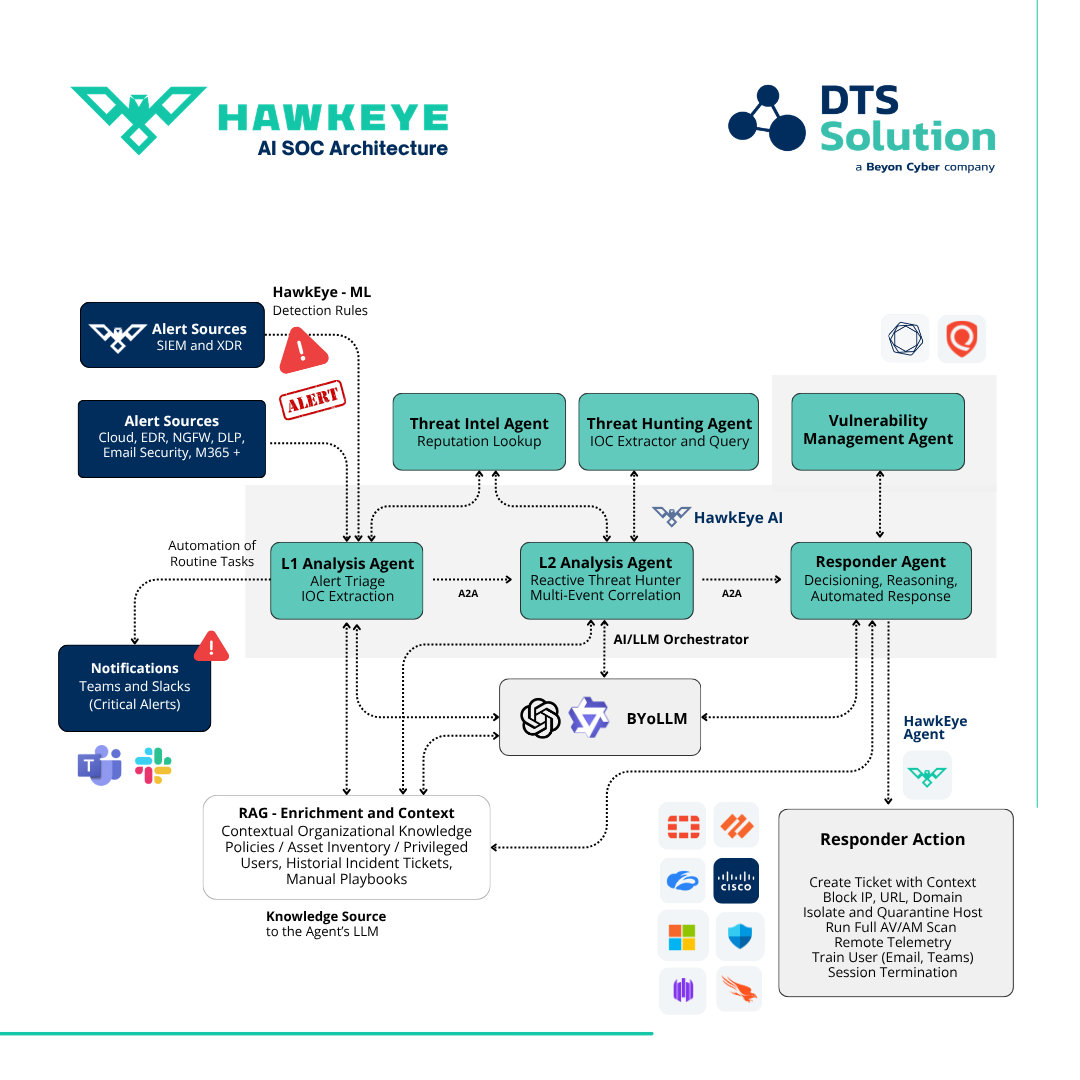
Multi Agent Architecture
Hawkeye deploys a team of 5 specialized AI agents, each built for a distinct role in the security operations workflow. From L1 triage and threat intelligence enrichment to L2 deep investigation and response recommendation, every agent operates autonomously yet collaboratively.
Together they cover detection, context gathering, behavioral analysis, and verdict delivery, ensuring no alert goes uninvestigated and no threat goes unnoticed.
Where AI shines!
- Alert Triage at Scale: Autonomously triaging hundreds of alerts in minutes, reducing analyst workload and eliminating alert fatigue.
- Explainable Verdicts: Delivering clear, evidence-backed decisions with full reasoning that analysts can trust and act on.
- Multi-Agent Investigation Deploying specialized AI agents (L1 Triage, Threat Intel, L2 Investigation) that collaborate to investigate alerts end-to-end without human intervention.
- Mean Time to Respond: Compressing detection-to-response timelines from hours to seconds, keeping SOC teams ahead of active threats.
- Contextual Threat Correlation: Connecting the dots across identity, cloud, network, and endpoint signals to surface the threats that matter most.